Ella McManus, a recent nursing graduate based in Saskatoon, Sask., experienced having her online identity stolen from her for the very first time this past summer. It was a normal weekday until a friend had contacted her asking about the odd behaviour of posting Bitcoin propaganda on her Instagram story. Of course, it wasn’t her posting those things, but a hacker who had managed to invade her account, pretending to be her. In that moment, McManus only felt one thing—pure panic. Though she didn’t post often, the knowledge that a stranger had taken full control over her account and had access to her pictures and private messages was incredibly unnerving.
All sorts of questions started filling her mind. Who hacked her account? What did they want? What would they do with her information? McManus had avoided reusing passwords across social media platforms, used two-factor authentication, and still she had her account compromised. At the time, she was unsure if she would regain access, which made her experience seem all the more terrifying—she says she felt completely powerless.
“I cried a lot. It’s a huge thing when somebody invades your privacy like that. I was posting on Instagram like once a year at the max, but it was honestly my way of connecting with people, and a lot of it was connecting with people in school for projects or whatever,” she said. “Not being able to access that really freaked me out; it’s a complete invasion of your privacy and personal life. Instagram is such a huge platform to share your personal life on, and when that happens, it really changes your mindset.”
She knew that having any online presence comes with a risk of getting hacked or having your identity breached in some way, but experiencing it first-hand gave her new insights into how unfriendly the internet really is. Even after reaching out to Instagram’s help service and reporting her own account, it still took a few days for her to regain access and control.
“It really opens your eyes and makes you want to use other mediums to communicate with your friends.”
“The best question you can ask yourself is, ‘How am I controlling my information?’ It turns out there is actually a lot in your control.”
Mike Gropp is a Senior Cybersecurity Advisor and Rogers Cybersecure Catalyst at Toronto Metropolitan University. He notes that other common ways online hackers are stealing identity information are via public dumps of compromised information from previous breaches or by buying information from data brokers. Scarily enough, Gropp adds that some hackers simply collect the public information they see displayed on social media accounts.
A recent Canadian study says that 62 per cent of cyberattacks are due to data encryption and email-based hacks.
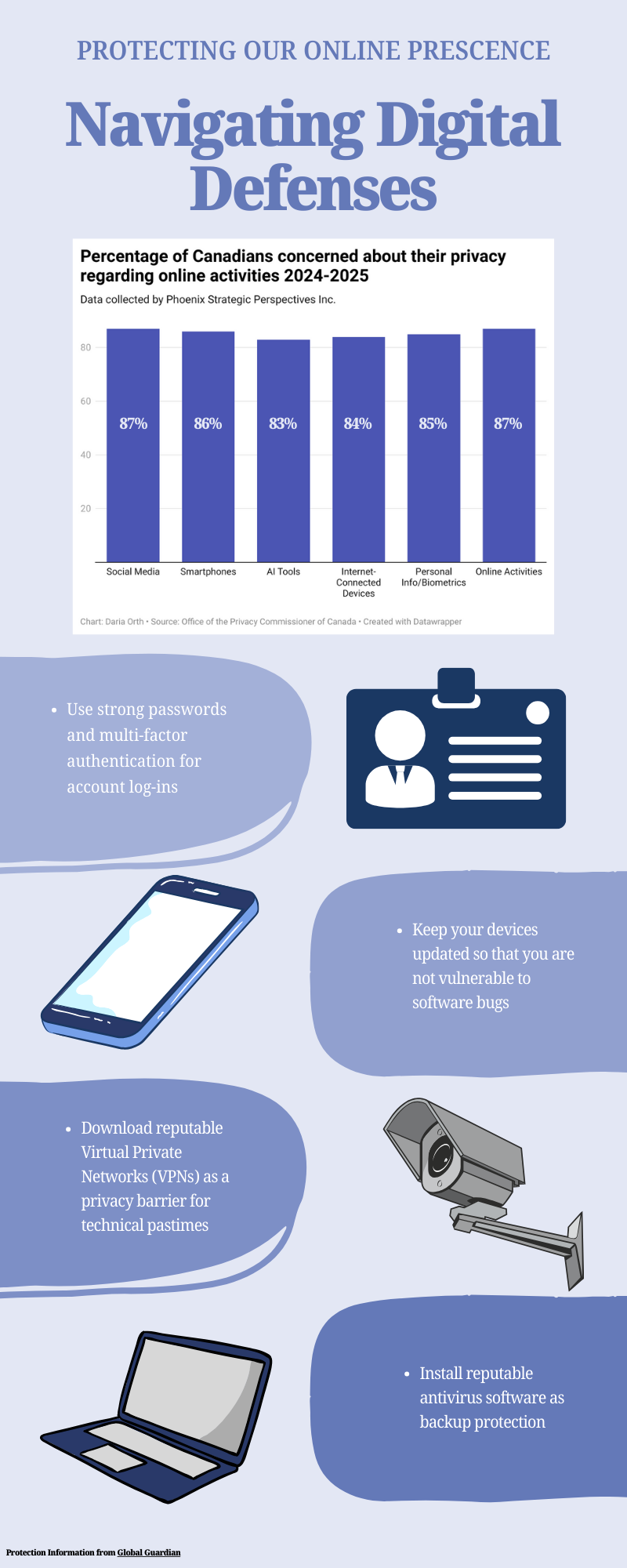
McManus discovered her Instagram account was hacked after her friend alerted her about suspicious activity on her profile, but there are other ways to check for privacy breaches in online accounts. Gropp explains that banking accounts will often show signs of being compromised with unfamiliar charges or withdrawals in bank and credit card statements, new accounts appearing that you never created, being denied credit for applications you didn’t make, receiving debt collection calls for unknown debts, or bills and tax documents for services you never received. For any online account, unexpected password changes, getting locked out, receiving notifications about suspicious login attempts, or receiving mail being sent from unknown senders are all indicators that your personal information could be threatened. He also warns to be careful with public Wi-Fi networks.
“Avoid it for sensitive operations like banking. For normal usage, use a trusted VPN to encrypt your internet traffic, keep your device firewalls turned on, and turn off sharing features like AirDrop or file sharing. Make sure your device doesn’t automatically connect to available Wi-Fi networks,” Gropp says.
Beyond strong passwords, he encouraged regularly checking privacy settings in online accounts and keeping devices and apps up to date. One of the most important things within our own control is educating ourselves on scams in order to defend ourselves from hacking strategies.
“These practical actions create strong layers of defense, giving you more control over who accesses your information and helping you stay ahead of cybercriminals.”
WHAT ELSE TO LOOK FOR
And if monitoring your private accounts wasn’t enough, there’s also the worry of cameras using Facial Recognition Technologies (FRT) that can pick up on personal data from just your face. FRT is a type of biometric technology that uses Artificial Intelligence (AI) to help analyze specific facial features of a person. A notable case in 2020 by CBC revealed that the real estate company Cadillac Fairview was using FRT embedded inside digital information kiosks at popular malls in Canada.
FRT can be scary, and not everyone may feel comfortable being monitored in certain public spaces. Some people are more private than others, and with deepfakes becoming more and more problematic, it’s a justified fear. The Alberta Law Enforcement Response Team (ALERT) reported that a 17-year-old boy used AI to create explicit and harmful images and videos of teenage girls in various Calgary high schools. With this kind of cyberbullying and sexual harassment, how can anyone not be slightly afraid of where their face ends up?
A report by Gartner, a technology consulting company, predicts that by next year, cybercriminals will be able to use deepfakes for identity verification, and facial biometrics will no longer be considered an ethical security measure.
“Biometrics are an excellent security feature when stored and used locally and securely. A great example of this is a Secure Enclave on your cell phone. This is a dedicated hardware-based security feature designed to isolate and protect sensitive data,” says Gropp. “Still, biometrics like voice recognition in the age of AI are a poor idea. Deepfakes and the continued cat-and-mouse game between attackers and defenders mean we don’t have a straightforward answer when it comes to the authentication request: yes or no.”
FASHION OR A SHIELD?
Clothing brands and fashion designers are now coming up with innovative ways to protect your personal identity with the clothes you wear on your body. Germany-based URBAN PRIVACY, and Italy-based Cap_able are companies that specialize in fabricating clothing that hides you from FRT camera scanners. Who knew your outfit could become a shield against AI privacy violations?
“I wanted to give people a way to choose when and how to be seen. Clothing is the most immediate form of identity expression, so it felt natural to transform it into a space of agency—where visibility becomes optional, not imposed,” said Rachele Didero, founder and designer of Cap_able.
Jordan Kidney, a professor at Mount Royal University in the faculty of science and technology, believes that AI and biometric technologies are great tools if used responsibly, but can be a nightmare in the wrong hands. He agrees that wearing FRT-suppressing clothing is a good idea, especially with the knowledge of possibly being under surveillance.
Nicole Scheller, fashion designer and creative director of URBAN PRIVACY, first started reflecting on what personal information she was sharing and leaving behind during her time studying at university. She started to pick up on how mindlessly people handled personal information. From there, she wanted to create something that could act as a privacy barrier, and suddenly, a bachelor’s degree project blossomed into a brand.
“Facial recognition algorithms rely on recurring visual structures—they analyze proportions and spatial relationships, which make up our biometric identity. I use these same facial blueprints as the foundation for my designs. The patterns are close enough for systems to interpret them as faces, yet distant enough that humans don’t immediately recognize them as such,” said Scheller.
Scheller mainly works with blacks, greys, and whites so that FRT systems respond to the high contrast palette, which she says functions very similarly to a QR code. With URBAN PRIVACY’S Faception Reloaded collection, they use digital prints and sweatshirt fabrics for a modern city vibe.

PHOTO: COURTESY OF URBAN PRIVACY
“Of course—algorithms are constantly evolving. That’s why our patterns are, too: they’re becoming more face-like and complex. Not every system reacts the same way, but based on biometric principles, we can predict that many will. We obviously can’t test every system out there, but each project helps us learn and adapt,” she said.
While this is a great option for protecting our faces in public, it’s unfortunately not an absolute solution to the bigger picture. Living in a digital world makes privacy more challenging than ever, but staying educated and hyper-aware of how to avoid having your data stolen is a good start. That in mind, it’s incredible to know that there are clothing brands taking fashion and privacy into account.
“The best question you can ask yourself is, ‘How am I controlling my information?’ It turns out there is actually a lot in your control,” said Gropp.